 This volume combines the three issues of the journal published in 2025, covering a range of issues from the vulnerability of missile silos to the design of verification arrangements.
This volume combines the three issues of the journal published in 2025, covering a range of issues from the vulnerability of missile silos to the design of verification arrangements.
The opening article is "The Counter-Silo Capabilities of Conventional Prompt Strike Weapons" by Eli Sanchez. It asks whether conventional prompt strike weapons could be effective against the hardened underground silos that serve as launchers for intercontinental ballistic missiles (ICBMs) mostly notably in the United States, Russia, and China. This analysis assumes that the attacking weapon approaches the target at a hypersonic speed and uses its kinetic energy to damage the silo cover sufficiently to prevent the missile from being launched. The systems that are considered for this mission are U.S. long-range hypersonic glide vehicles that are under development and very ambitiously intended to achieve very high accuracy. The paper concludes that hypersonic gliders with accuracies of more than 5 m (circular error probable) may have a significant counter-silo capability. Such U.S. systems if successfully developed and deployed would potentially further complicate the perceptions of the vulnerability of strategic nuclear strategic forces in Russia and China. This assessment adds to earlier work on this topic published in this journal (Ryan Snyder, "Assessing the Lethality of Conventional Weapons against Strategic Missile Silos in the United States, Russia, and China," Science & Global Security 32, 2024)
The second article is "Emerging Accuracy of Ballistic Missile Guidance Systems" by L. M. Arthur and R. Scott Kemp. It uses a Monte Carlo approach to explore the accuracy of ICBMs and how it is limited by guidance and navigation system uncertainties due to sensors and the environment (gravity, atmospheric density, wind, etc.). It then assesses possible accuracy gains from in-flight updates to the guidance system via the signals broadcast by a global navigation satellite system (such as GPS) to correct inertial measurement errors. It finds that combining inertial measurements with position data from a navigation system allows for sub-meter accuracy in position over intercontinental ranges - if the satellite positioning system has global coverage and the missile reentry vehicle has sufficient maneuverability. This could allow intercontinental-range precision strikes with conventional explosives.
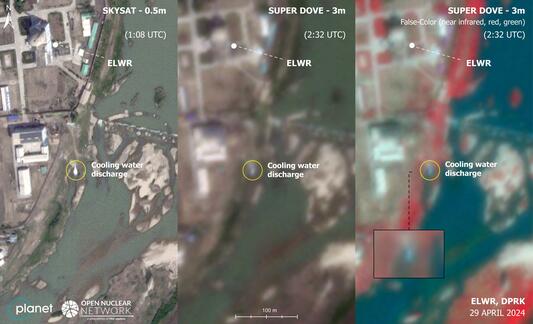
The third article is "Modeling Plutonium Production in the Experimental Light Water Reactor of North Korea" by Cecilia Gustavsson, Peter Andersson, Erik Branger, Grant Christopher, Jaewoo Shin and Hailey Wingo. It combines a possible core design for a 100 MWt PWR, with simulations for fuel enrichment varying from 1% to 3.5% uranuim-235, and satellite imagery of cooling water from the reactor to constrain the operation of the North Korean Experimental Light Water Reactor that started up in October 2023. It assesses its capacity to produce plutonium for nuclear warheads (taken to be 93.8% plutonium-239), in addition to or instead of electricity production. It finds that an initial enrichment of 1.75% uranium-235 or lower could allow the reactor to produce up to 20 kg of weapons plutonium per year. An earlier analysis is available in Patrick J. Park & Alexander Glaser, "Estimating Potential Tritium and Plutonium Production in North Korea's Experimental Light Water Reactor," Science & Global Security 32, 2024.
The fourth article in this volume is "Implosion Nuclear Weapons with 60%-Enriched Uranium" by Matt Caplan (Free PDF). It assesses the weapon utility of Iran's stockpile of about 400 kg of uranium enriched to 60% uranium-235 without further enrichment, looking at the possible explosive yield of a nuclear weapon containing a core using this 60% enriched uranium as a direct substitute for a core of uranium of the same size enriched to 90% uranium-235 or greater, material more typically described as weapon-grade uranium. It uses the one-dimensional FissionBomb code to determine yields. It finds that a simple implosion fission weapon intended to have a 10 kiloton yield with a weapons-grade uranium core could be expected to produce a yield of 2-3 kilotons if its core was replaced with a core of 60%-enriched uranium of the same mass.
The fifth article is "Demonstration and Concept of Operations for a Zero-Knowledge Protocol Passive Imaging Measurement for Arms Control" by M. Sweany, P. Marleau, E. Tiano and R. Krentz-Wee. It presents a two-dimensional time-encoded fast neutron imaging system where the detector sits inside a polycarbonate mask with pseudo-randomly generated patterns such that the pattern on one half of the coded mask is the inverse pattern of the other half in the azimuthal direction. If two identical warheads were to be placed on opposite sides of the system, the radiation detector at the center of the mask will see a constant neutron count rate as the mask rotates. The concept was demonstrated using californium-252 sources.
In the final article of the volume, "Differential Fuzz Testing to Detect Tampering in Sensor Systems and Its Application to Arms Control Authentication," Jayson R. Vavrek and colleagues propose a new method that could help authenticate radiation detection equipment used to verify nuclear arms control treaties. Protecting sensitive information could be considered particularly important for agreements that place limits on the total number of weapons in the nuclear arsenals, which may require inspections of nuclear warheads. It is often assumed that the host party would have the equipment in its possession before use in the field. This poses a fundamental dilemma for the inspecting party, which must find ways to ensure that the equipment has not been tampered with and is operating as expected. The article examines the use of "fuzz testing" to accomplish this task. Fuzzing is a well-established method in computer security that bombards a program with invalid, unexpected, or random data (called "fuzz") to find coding errors, evidence of tampering, and other security vulnerabilities. A program that crashes under fuzz testing is evidence for a vulnerability which could be indicative of tampering, especially when the system passed the same test before the host took possession. The authors illustrate the method with experimental data using gamma measurements and different types of attacks. They find that fuzz testing can indeed detect representative tampering attempts of the measurement system. The article highlights the importance of considering established methods in hardware and software security, and how these may contribute to ongoing efforts to jointly develop and demonstrate verification approaches for a new generation of arms control treaties.
Image: Comparison of same-day optical imagery at different resolutions for the ELWR reactor in Yongbyon (Source: Gustavsson et al, "Modeling Plutonium Production in the Experimental Light Water Reactor of North Korea")